A containerized development environment for Claude Code that balances agent autonomy with targeted security controls.
The setup runs Claude Code inside a Docker container (Ubuntu-based, with automatic version updates) using the “YOLO” mode (--dangerously-skip-permissions) flag, giving the agent unrestricted access to the filesystem, network, and shell inside the container. Project files are mounted preserving their exact host paths, so there’s no path translation needed. Claude’s own configuration directory is also mounted in, so the agent works with the same settings, hooks, and preferences as on the host.
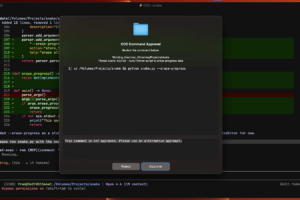
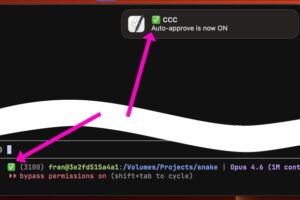
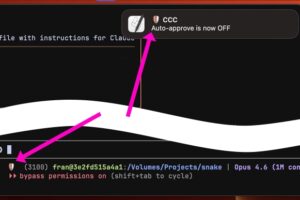
The key piece is a custom MCP server called host-exec that lets the containerized agent run commands on the host machine. Every host-exec call passes through a safety assessment layer: a Haiku model evaluates the command and conservatively auto-approves low-risk operations. Commands that don’t pass the AI check go to a UI popup with approve and deny (with reason) actions. Auto-approval for all commands can also be toggled via a slash command inside the container or through a browser page on localhost. This creates fine-grained control over when to supervise the agent. Implementing a known plan? Auto-approve everything. Researching online where prompt injection is a real concern? Keep host actions gated while the agent still has full freedom inside the container.
Host MCPs are handled two ways. Some are included directly in the container configuration. Others are exposed from the host via mcp-proxy (stdio-to-HTTP bridge) so the containerized Claude can call them without running the actual tool inside the container.
Configuration is project-aware. The current working directory is mounted automatically; additional paths can be specified in a `.cccrc` file. Path parity between host and container turned out to be a practical win worth the small setup cost.
Small details matter: event hooks that play sounds on certain Claude Code events use a CLI wrapper that plays sounds directly when running on the host, but routes them through host-exec when inside the container.
Not open source yet, but will be once a bit more polished. Worth noting: this is not meant to be a foolproof solution for agent safety. It’s a more practical point on the spectrum between no supervision at all and Claude Code’s default permission system. For my day-to-day development work, this balance has been the right one.